The Compute Famine Is No Longer a Forecast. OpenAI’s CFO confirmed they are passing on opportunities because there is not enough silicon. H100 rental prices just hit an 18-month high on the secondary market. Anthropic tightened session limits — 7% of users now hit walls that didn’t exist a month ago. AWS lost a $10 million Fortnite hosting contract because it could not guarantee capacity. This is the physical constraint expressing itself in dollars per hour: not a supply chain delay, not a logistics hiccup, but a hard ceiling on what can be computed today regardless of willingness to pay. Meanwhile Alibaba closed-sourced Qwen, its open-weight flagship, confirming that the remaining frontier is being hoarded rather than shared. Kuaishou’s Kling AI reported $300 million in annualized video generation revenue — application-layer traction accumulating above an infrastructure layer that is actively choking. The stampede has arrived at the gate, and the gate is locked
.
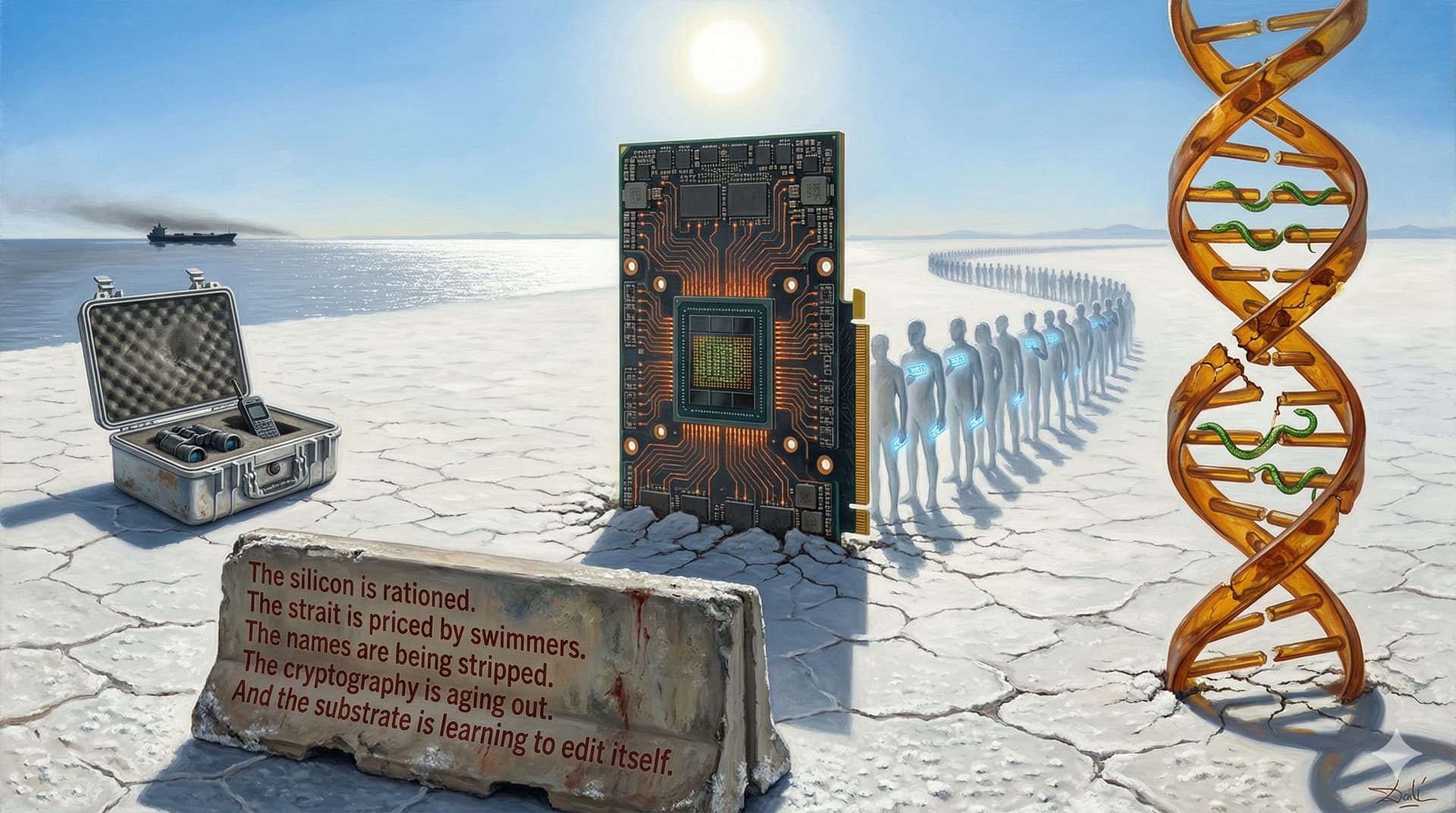
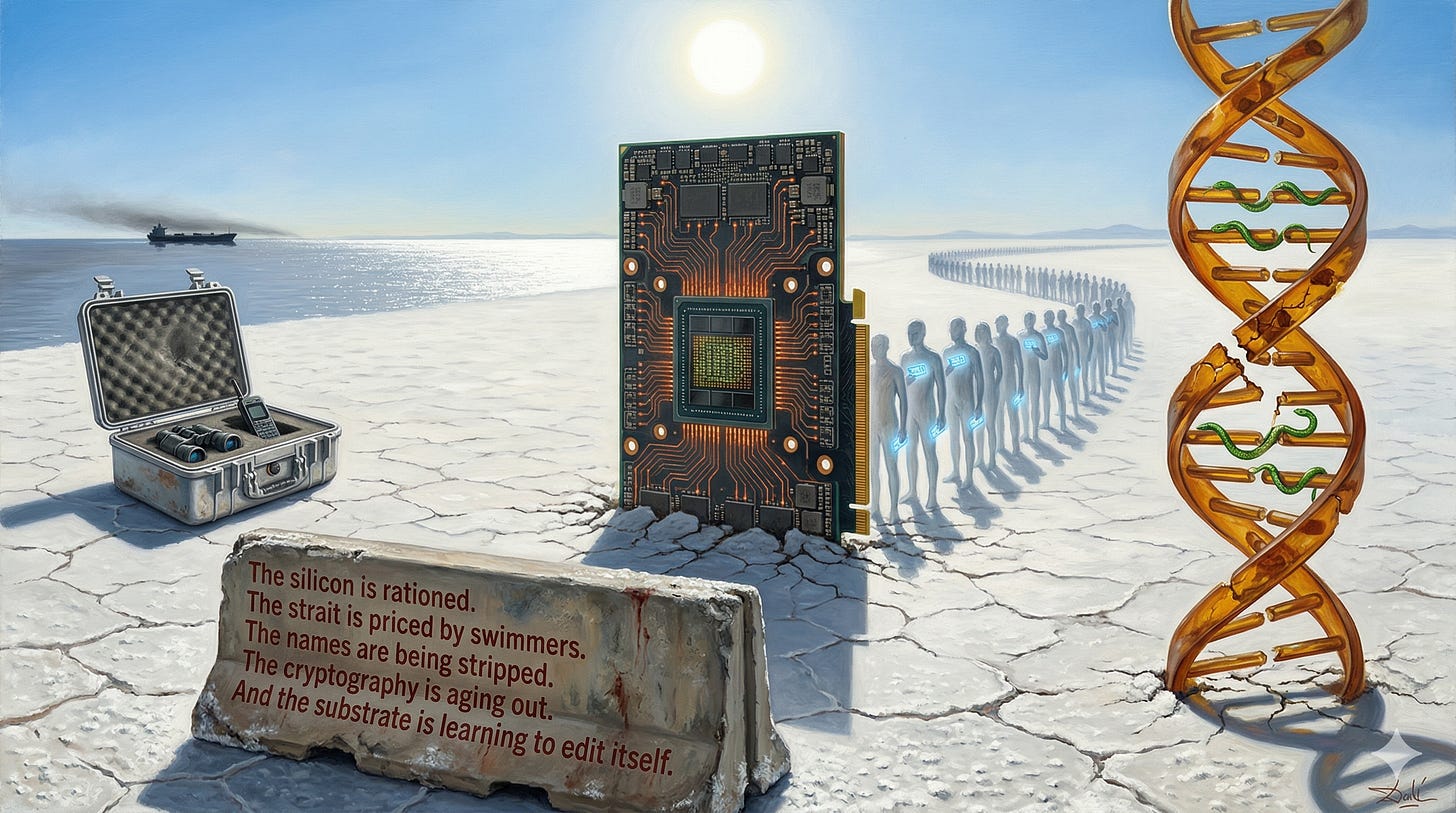
The Strait Is Being Priced by Swimmers. Citrini Research sent an analyst to Oman’s Musandam province — eighteen miles from the Iranian coast, Shahed drones overhead — to observe tanker traffic that AIS tracking data misses entirely. Half the shipping data is dark. The global commodity markets are trading on satellite imagery and Pentagon leaks while someone in a Pelican case is counting hulls from a shoreline inside the kill radius. The information asymmetry between a Bloomberg terminal and actual human observation of the Strait of Hormuz has never been wider. This is what “on-the-ground research” looks like when the ground is a peninsula jutting into an active war zone, and it is a reminder that the most valuable data in a crisis is always the data that the infrastructure cannot capture.
The Pseudonymous Internet Is Dying. LLMs can now deanonymize Hacker News users and Anthropic interview subjects at 68% recall and 90% precision — matching in seconds what a human investigator would need hours to achieve. The practical obscurity that protected online identity for two decades is collapsing under the weight of stylometric inference. The threat model for digital privacy requires reconstruction from first principles. Cancel culture may fade as retaliation becomes algorithmically certain — but so will honest discourse under any name but your own. The internet’s last decade of toxic anonymity was subsidized by identity friction. That subsidy is being revoked, and nothing is replacing it except silence or the legal name.
Cryptographic Trust Now Has an Expiration Date. Google published a lower-overhead implementation of Shor’s algorithm for breaking 256-bit elliptic curve cryptography. Caltech demonstrated fault-tolerance at reduced overhead. Scott Aaronson compared the moment to Frisch and Peierls calculating the critical mass for U-235 in 1940 — knowledge that reorganizes the strategic landscape before the weapon exists. Cybersecurity practitioners pushed back on the nuclear analogy, arguing that publishing the results may be the only mechanism to force migration to quantum-resistant systems before the window closes. The modern financial system, the military command chain, and every encrypted message on earth runs on the assumption that factoring large numbers is hard. That assumption now has a shelf life measured in years, not decades.
The Biological Substrate Is Being Reverse-Engineered in Bulk. Meta translated an entire graduate mathematics textbook into Lean formal proofs using 30,000 parallel LLM agents — proof-checking as a parallelizable compute job. Open-source labs trained mRNA language models across 25 species for $165. Gladstone and Nvidia unveiled MaxToki, trained on a trillion gene tokens to simulate cell-state trajectories across the human lifespan. CU Boulder discovered para-tyramine-O-sulphate in python blood — an appetite suppressor that lets snakes fast for months while remaining metabolically intact, and it works in obese mice without the nausea that plagues GLP-1 drugs. The optimization loops that produced us are now being run in silicon, and the silicon is finding solutions the evolution took four billion years to miss.
The Agents Are Breaching the Fourth Wall. OpenAI’s Codex now lives inside DOOM — walk up to a terminal in the game, ask it to write code, and it does. The boundary between tool and environment is dissolving into a membrane. Developers discovered that making Claude speak like a caveman cuts token usage 75% while preserving task accuracy — efficiency through deliberate linguistic regression. Microsoft has applied the Copilot brand to 78 separate products, producing Copilots nested inside Copilots and a physical keyboard key for summoning them, while quietly labeling the output “for entertainment purposes only.” The application layer is where capability outruns its own packaging, and the packaging has started to eat itself.
The silicon is rationed.
The strait is priced by swimmers.
The names are being stripped.
The cryptography is aging out.
And the substrate is learning to edit itself.
╔════════════════════════════════════════════════╗
║ 📡 KINETIC RESONANCE — April 5, 2026 ║
╚════════════════════════════════════════════════╝
▶ COMPUTE FAMINE / PHYSICAL CEILING
Named : $NVDA (H100 rentals at 18-month highs)
1st 🟢: $AMZN $MSFT $GOOGL — hyperscalers with captive
capacity; demand exceeds physical supply
2nd 🟢: $VST $CEG — power bottleneck is the compute
bottleneck; utilities own the constraint
3rd 🟡: $AMD $INTC — potential share gain if execution
materializes; high uncertainty
▶ HORMUZ / GROUND-TRUTH PREMIUM
Named : —
1st 🟢: $XOM $CVX — US producers print while strait
tensions sustain elevated spreads
2nd 🟢: $FRO $STNG — tanker war premium per mile sailed;
$OKE $WMB — midstream export terminal exposure
3rd 🟡: $DSSI $LPG — smaller energy with asymmetric
optionality on sustained disruption
▶ QUANTUM THREAT / CRYPTO MIGRATION
Named : —
1st 🟢: $CRWD $PANW — post-quantum security migration
creates upgrade cycle across enterprise
2nd 🟡: $IBM — quantum hardware leadership but services
revenue muddies the signal
3rd 🔴: $QSI — pure-play quantum; thesis intact but
pre-revenue risk extreme
▶ PSEUDONYMITY COLLAPSE / IDENTITY INFRASTRUCTURE
Named : —
1st 🟢: $META $GOOGL — identity graphs appreciate as
deanonymization becomes trivial
2nd 🟢: $PLTR — surveillance/identity verification
infrastructure; government + enterprise
3rd 🔴: $RBLX $U — pseudonymous youth platforms face
regulatory and reputational repricing
▶ BIOTECH / SYNTHETIC BIOLOGY ACCELERATION
Named : $NVDA (MaxToki with Gladstone)
1st 🟢: $DNA $RXRX — synthetic bio platforms with
AI-enabled protein/gene design
2nd 🟢: $NVO $LLY — GLP-1 incumbents; python blood
compound is complementary or existential
3rd 🟡: $AMGN $VRTX — genomics pipelines accelerated
by LLM-driven formal proof translation